3 Videos for JWT IV

This video requires PentesterLab PRO
GO PRO
JWT IV - Introduction
In this video, we cover the exercise JWT 4 from the blue badge series. You'll learn about the key ID parameter in JWT headers and how its injection can lead to remote command execution.
This video requires PentesterLab PRO
GO PRO
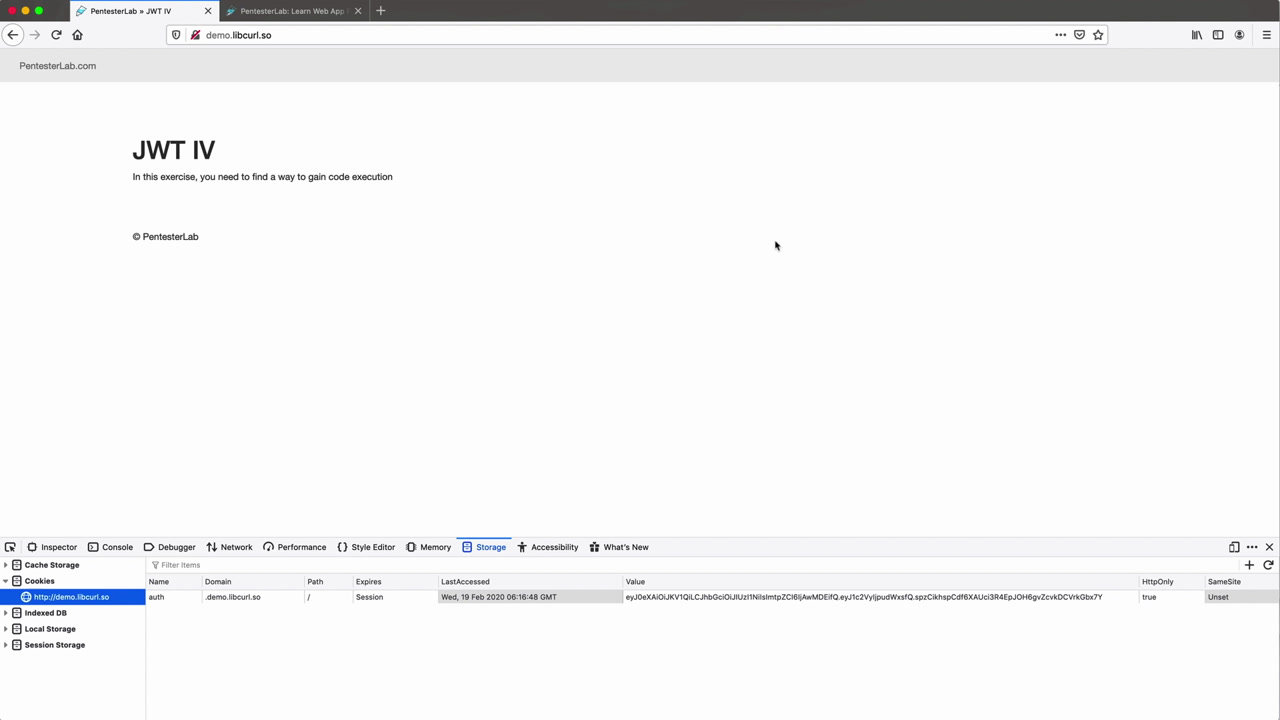
JWT IV - Exploitation
In this video, we cover the exploitation technique for JWT (JSON Web Token) vulnerabilities as part of the blue badge exercises. We explore how to manipulate the key ID in the JWT header to achieve command execution through improper use of Ruby's open function.
This video requires PentesterLab PRO
GO PRO
JWT IV: Exploitation in Python 2 and 3
In this video, we delve into the JWT IV exercise from the blue badge series on PentesterLab. We demonstrate how to gain code execution using Python 2 and 3 by exploiting JWT tokens.
