4 Videos for CVE-2007-1860: mod_jk double-decoding

This video requires PentesterLab PRO
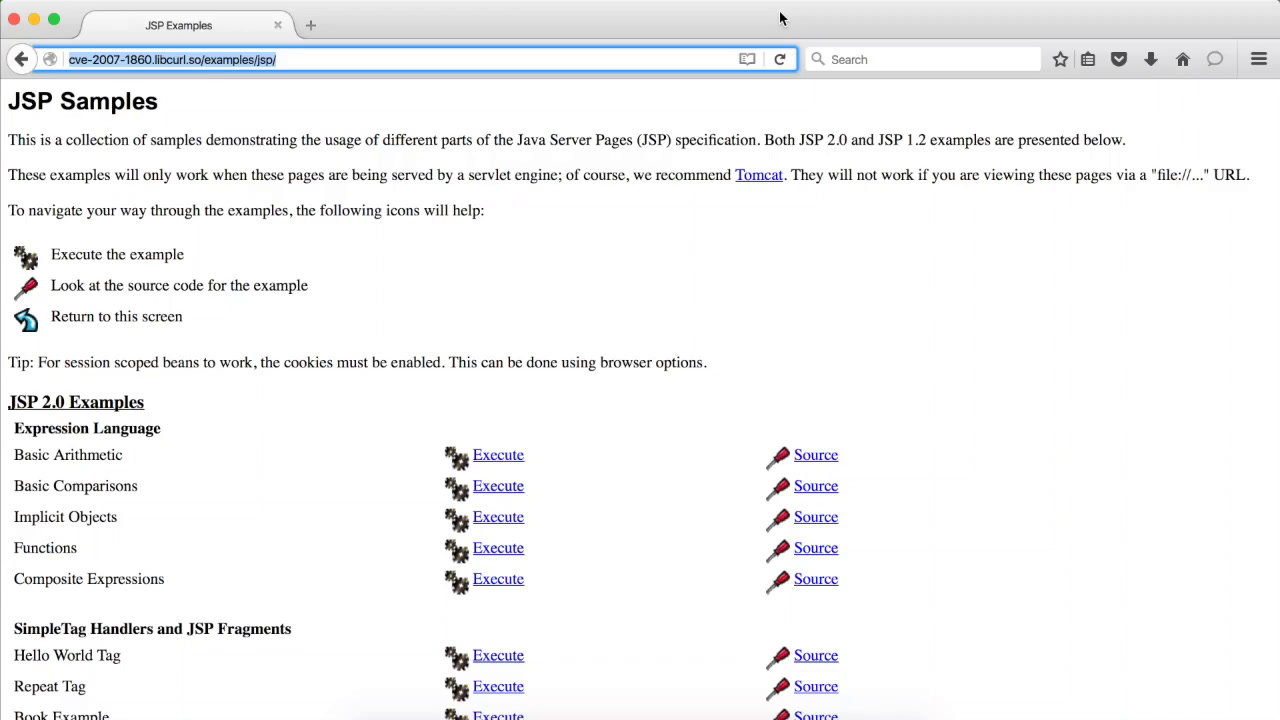
GO PROIn this video, we will explore the challenge CVE-2007-1860 as part of the white badge. We will exploit MOD_JK to gain code execution on a Tomcat server.
This video requires PentesterLab PRO
GO PROIn this video, we explore the exploitation of CVE-2007-1860 in the online environment using Tomcat 7.0, highlighting the differences in security mechanisms compared to the ISO version with Tomcat 6.0. We demonstrate how to bypass CSRF protection and successfully deploy a web shell.
This video requires PentesterLab PRO
GO PROThis video covers an analysis of CVE-2007-1860, a double URL decoding vulnerability that affected Apache mod_jk in 2007. The issue arises from both Apache and Tomcat performing URL decoding, allowing attackers to bypass restrictions.
This video requires PentesterLab PRO
GO PROIn this video, we explore the exploitation of CVE-2007-1860, a vulnerability in Apache mod_jk. We'll demonstrate how to bypass URL encoding to access restricted areas of a Tomcat server.
