JWT VIII - Exploitation
This video requires PentesterLab PRO
GO PRO
JWT VIII - Exploitation
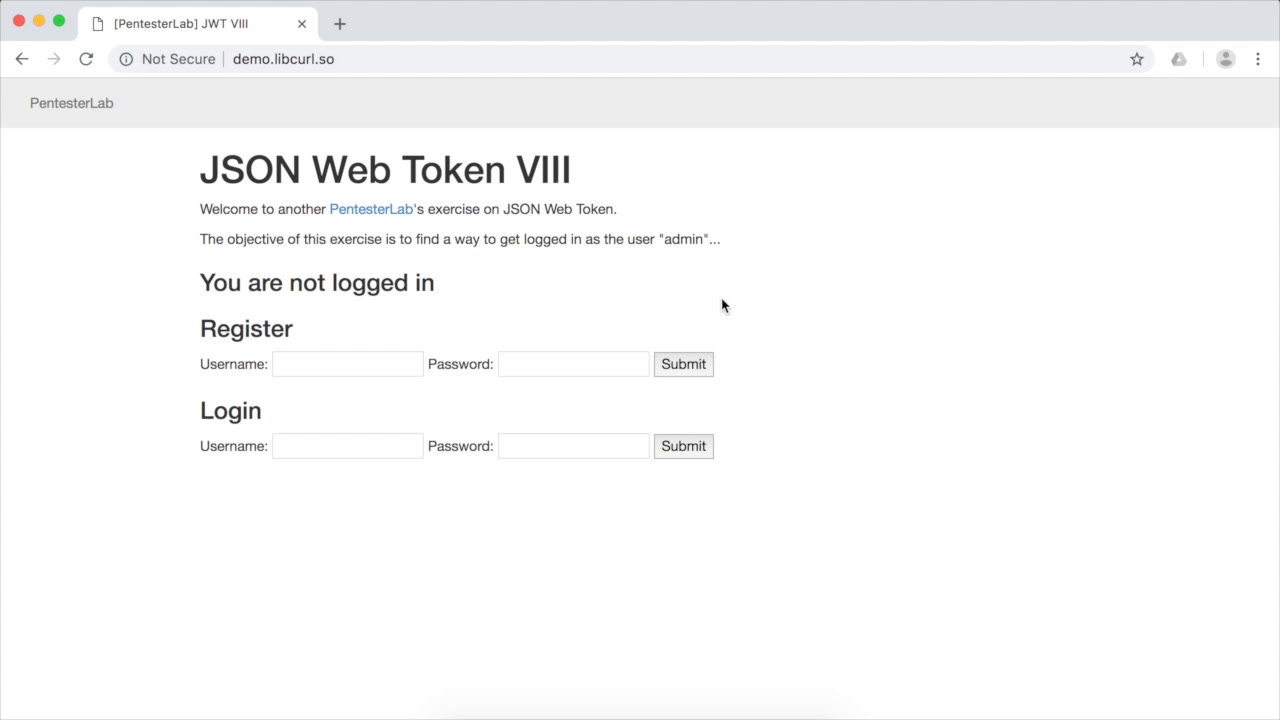
In this video, we explore the exploitation of JSON Web Tokens (JWT) through a practical exercise. We'll cover the process of forging a token to bypass authentication and gain admin access.
